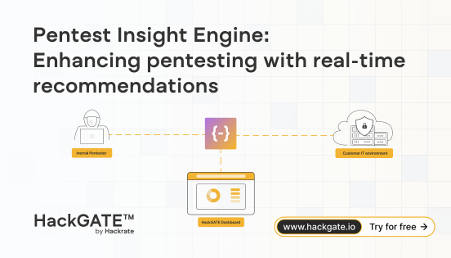
Advanced project analytics
Simplify compliance audits with HackGATE
As a transparent solution, HackGATE operates independently from the penetration testers. Integrated with a leading Security Information and Event Management (SIEM) system.
Identifies attack types and generates audit reports about the security testing
Helps you to ensure comprehensive assessment and security control is effective
Logs all activities during the pentest project, ensuring accountability






.avif)